What is the best way to pass the Cisco CCNP Security 300-210 exam? (First: Exam practice test, Second: leads4pass Cisco expert.) You can get free Cisco 300-210 exam practice test questions here. Or choose: https://www.leads4pass.com/ccnp-security.html Study hard to pass the exam easily!
Table of Contents:
- Latest Cisco CCNP Security 300-210 google drive
- Effective Cisco CCNP Security 300-210 exam practice questions
- Related 300-210 Popular Exam resources
- leads4pass Year-round Discount Code
- What are the advantages of leads4pass?
Latest Cisco CCNP Security 300-210 google drive
[PDF] Free Cisco 300-210 pdf dumps download from Google Drive: https://drive.google.com/open?id=1ZIPFR3Qt_JvjHvAA7SxJGD3-Hxa8TpT5
300-210 SITCS – Cisco:https://www.cisco.com/c/en/us/training-events/training-certifications/exams/current-list/sitcs.html
This exam tests on advanced firewall architecture and configuration with the Cisco next-generation firewall, utilizing access and identity policies.
Some older technologies have been removed, such as the Cisco Intrusion-prevention system & Firewall CX. Coverage was added for Cisco NGFW,
Cisco Firepower NGIPS and Cisco AMP (Advanced Malware Protection), as well as Web and Email Security solutions.
Latest updates Cisco CCNP Security 300-210 exam practice questions
QUESTION 1
When the WSA policy trace tool is used to make a request to the proxy, where is the request logged?
A. proxy logs
B. access logs
C. authentication logs
D. The request is not logged
Correct Answer: B
QUESTION 2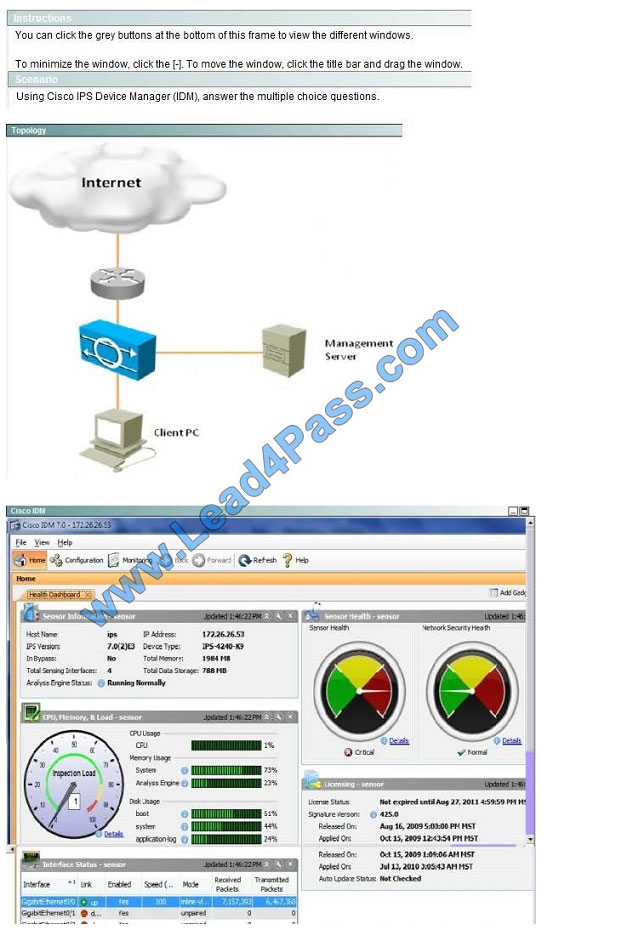
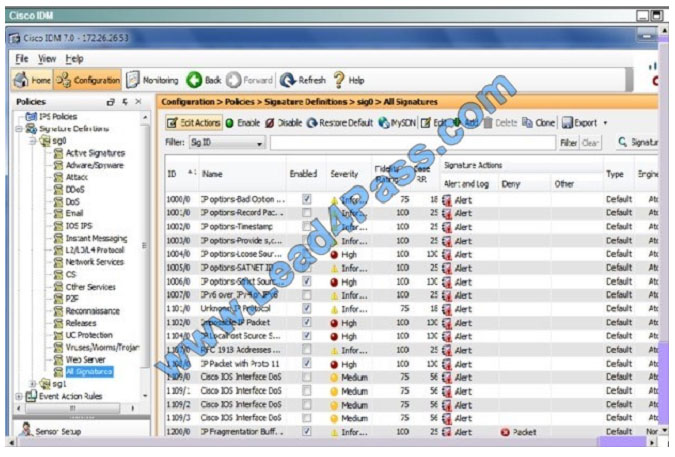
Which two statements about Signature 1104 are true? (Choose two.)
A. This is a custom signature.
B. The severity level is High.
C. This signature has triggered as indicated by the red severity icon.
D. Produce Alert is the only action defined.
E. This signature is enabled, but inactive, as indicated bythe/0 to that follows the signature number.
Correct Answer: BD
This can be seen here where signature 1004 is the 5th one down:
QUESTION 3
An engineer is using the policy trace tool to troubleshoot a WSA. Which behavior is used?
A. External DLP policies are evaluated by tool
B. Socks policies are evaluated by tool
C. Web proxy
Correct Answer: C
QUESTION 4
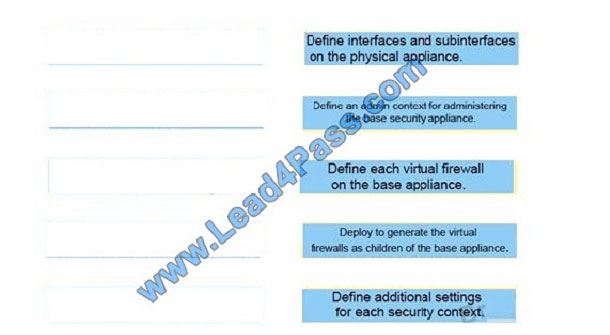
Drag and drop the steps on the left into the correct order on the right to configure a Cisco ASA NGFW with multiple
security contexts.
Select and Place: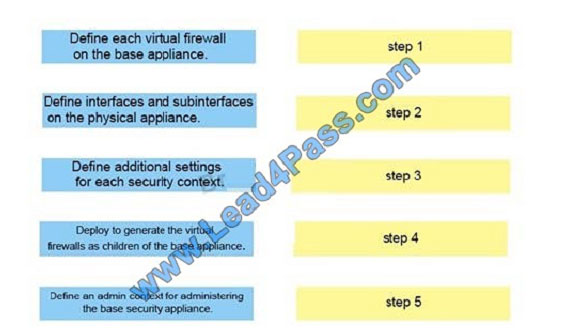
Correct Answer:
QUESTION 5
Which five system management protocols are supported by the Intrusion Prevention System? (Choose five.)
A. SNMPv2c
B. SNMPv1
C. SNMPv2
D. SNMPv3
E. syslog
F. SDEE
G. SMTP
Correct Answer: ABCFG
QUESTION 6
Which two statements about devices within a Cisco ESA cluster are true? (Choose two.)
A. Clustered systems must consist of devices in the same hardware series.
B. Clustered devices can communicate via either SSH or Cluster Communication Service.
C. Clustered devices can communicate only with Cluster Communication Service.
D. In-the-cloud devices must be in a separate cluster from on-premise devices.
E. Clustered devices can run different versions of AsyncOS.
Correct Answer: AB
QUESTION 7
Which two actions can be used in an access control policy rule?
A. Block All
B. Monitor
C. Trust Rule
D. Discover
E. Block with Reset
Correct Answer: BE
https://www.cisco.com/c/en/us/td/docs/security/firepower/601/configuration/guide/fpmc-config-guide-v601/Getting_Started_with_Access_Control_Policies.pdf
QUESTION 8
Which Cisco ASA platform should be selected if the requirements are to support 35,000 connections per second,
600,000 maximum connections, and traffic shaping?
A. 5540
B. 5550
C. 5580-20
D. 5580-40
Correct Answer: C
QUESTION 9
An engineer is trying to configuring email encryption on Cisco ESA. Which technology could be used as a key server?
A. Cisco Registered Envelop Service
B. Local CA
C. Cisco Talos Services
D. Cisco ISE
Correct Answer: A
QUESTION 10
Which Cisco WSA is intended for deployment in organizations of up to 1500 users?
A. WSA S370
B. WSA S670
C. WSA S370-2RU
D. WSA S170
Correct Answer: D
QUESTION 11
Which two types of security applications can be installed on a Firepower Security Appliance 4100? (Choose two.)
A. Cisco Firepower
B. Cisco Firepower Management Center
C. Cisco Firepower threat Defense
D. Cisco ASA
E. Cisco Firepower Appliance
Correct Answer: BC
QUESTION 12
Which proxy mode must be used on Cisco WSA to redirect TCP traffic with WCCP?
A. redirection
B. transparent
C. proxy gateway
D. forward
Correct Answer: B
QUESTION 13
A system administrator wants to know if the email traffic from a remote partner will activate special treatment message
filters that are created just for them. Which tool on the Cisco Email Security gateway can you use to debug or emulate
the flow that a message takes through the work queue?
A. the message tracker interface
B. centralized or local message tracking
C. the CLI findevent command
D. the trace tool
E. the CLI grep command
Correct Answer: D
Related 300-210 Popular Exam resources
| title | youtube | Cisco | leads4pass | leads4pass Total Questions | |
|---|---|---|---|---|---|
| Cisco CCNP Security | leads4pass 300-210 dumps pdf | leads4pass 300-210 youtube | 300-210 SITCS – Cisco | https://www.leads4pass.com/300-210.html | 455 Q&A |
| leads4pass 300-206 dumps pdf | leads4pass 300-206 youtube | 300-206 SENSS – Cisco | https://www.leads4pass.com/300-206.html | 461 Q&A | |
| leads4pass 300-208 dumps pdf | leads4pass 300-208 youtube | 300-208 SISAS – Cisco | https://www.leads4pass.com/300-208.html | 478 Q&A | |
| leads4pass 300-209 dumps pdf | leads4pass 300-209 youtube | 300-209 SIMOS – Cisco | https://www.leads4pass.com/300-209.html | 445 Q&A | |
| 300-710 SNCF – Cisco | leads4pass brain dumps | 60 Q&A | |||
| 300-715 SISE – Cisco | leads4pass brain dumps | 60 Q&A | |||
| 300-720 SESA – Cisco | leads4pass brain dumps | 60 Q&A | |||
| 300-725 SWSA – Cisco | leads4pass brain dumps | 60 Q&A | |||
| 300-730 SVPN – Cisco | leads4pass brain dumps | 60 Q&A | |||
| 300-735 SAUTO – Cisco | leads4pass brain dumps | 60 Q&A |
leads4pass Year-round Discount Code
What are the advantages of leads4pass?
leads4pass employs the most authoritative exam specialists from Cisco, Microsoft, CompTIA, IBM, EMC, etc. We update exam data throughout the year. Highest pass rate! We have a large user base. We are an industry leader! Choose leads4pass to pass the exam with ease!
Summarize:
It’s not easy to pass the Cisco 300-210 exam, but with accurate learning materials and proper practice, you can crack the exam with excellent results. https://www.leads4pass.com provides you with the most relevant learning materials that you can use to help you prepare.